
Amazon.com: Programming Internet Email: Mastering Internet Messaging Systems eBook : Wood, David: Kindle Store

Amazon.com: Programming Internet Email: Mastering Internet Messaging Systems eBook : Wood, David: Kindle Store
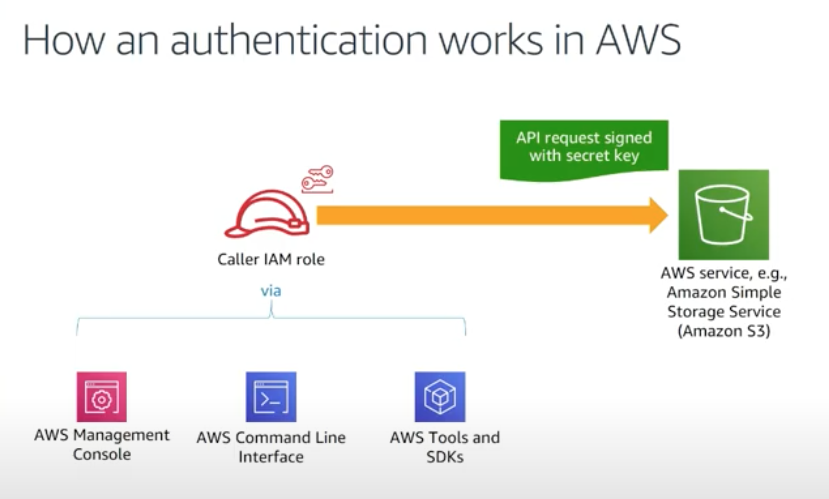
AWS Identity and Access Management (IAM) Policies, sts AssumeRole, and delegate access across AWS accounts - 2021
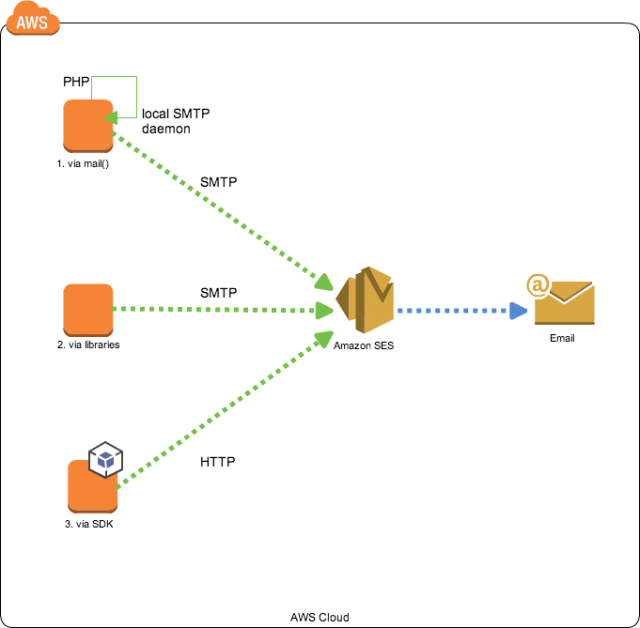



![amazon_ses_smtp_server_configuration [LUCY] amazon_ses_smtp_server_configuration [LUCY]](https://wiki.lucysecurity.com/lib/exe/fetch.php?w=400&tok=2da91c&media=amazon-ses2.png)






![amazon_ses_smtp_server_configuration [LUCY] amazon_ses_smtp_server_configuration [LUCY]](https://wiki.lucysecurity.com/lib/exe/fetch.php?w=600&tok=76ee50&media=amazon-ses.png)
